Write Up – JP 8000
Write-up bisa dibaca langsung di halaman ini atau diunduh sebagai file PDF.
Write Up – JP 8000
Write Up – JP 8000
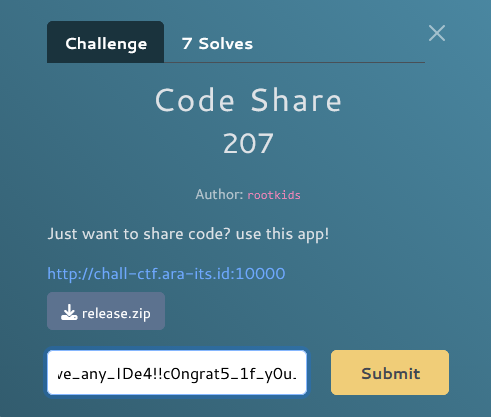
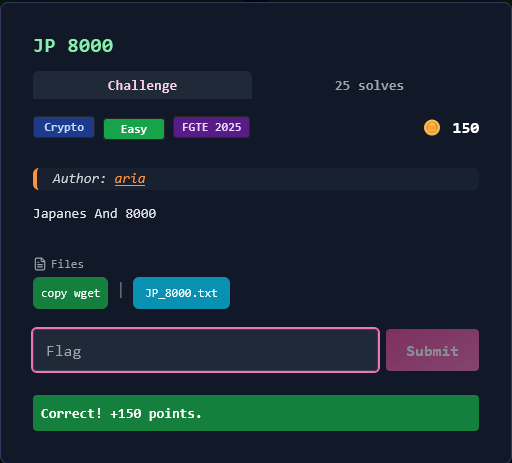
Challenge Overview
Category: Crypto
Difficulty: Easy
Author: aria
Challenge dengan nama "Japanese And 8000" ini melibatkan multiple encoding layers yang menggunakan Japanese character encoding (CP932), Morse code, dan Base32. Angka "8000" mengacu pada encoding Shift-JIS/CP932 yang menggunakan code points di sekitar range 8000-an dalam hex.
Format flag:
FGTE{...}
Files Given
1. Encoded Data (JP_8000.txt)
QNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6F7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6F7HCWUQNPYGYUDK2BYLA3IQNRIGZ4DNCBWFA3HRPZYVVEDL6BWFA2WQOCYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBV7A3CQNLIHBMDL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWBWRA3CQNTYX44K2SBV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBWRA3CQNTYG2EDMKBWPA27QNRIGVUDQWF7HCWUQNUIGYUDM6F7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPC7TRLKIG2EDMKBWPA27QNRIGVUDQWBWRA3CQNTYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDL6BWFA2WQOCYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWBWRA3CQNTYX44K2SBV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDNCBWFA3HRPZYVVEDL6BWFA2WQOCYG2EDMKBWPA27QNRIGVUDQWF7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBWRA3CQNTYG2EDMKBWPA27QNRIGVUDQWBV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6F7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBML6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBV7A3CQNLIHBML6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6F7HCWUQNPYGYUDK2BYLA3IQNRIGZ4DL6BWFA2WQOCYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPC7TRLKIG2EDMKBWPA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBV7A3CQNLIHBMDNCBWFA3HRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBWRA3CQNTYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNPYGYUDK2BYLC7TRLKIG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDL6BWFA2WQOCYG2EDMKBWPA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6F7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPC7TRLKIGX4DMKBVNA4FRPZYVVEDNCBWFA3HQNUIGYUDM6BWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BWRA3CQNTYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNPYGYUDK2BYLC7TRLKIG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6F7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4L6OFNJA3IQNRIGZ4DL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDL6BWFA2WQOCYGX4DMKBVNA4FQNUIGYUDM6F7HCWUQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPC7TRLKIG2EDMKBWPA27QNRIGVUDQWBV7A3CQNLIHBMDNCBWFA3HRPZYVVEDL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDL6BWFA2WQOCYG2EDMKBWPC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLC7TRLKIG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6F7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPC7TRLKIGX4DMKBVNA4FRPZYVVEDNCBWFA3HQNUIGYUDM6BWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA27QNRIGVUDQWBWRA3CQNTYX44K2SBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4L6OFNJA3IQNRIGZ4DL6BWFA2WQOCYGX4DMKBVNA4FQNUIGYUDM6F7HCWUQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBWRA3CQNTYGX4DMKBVNA4FRPZYVVEDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNUIGYUDM6BWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPC7TRLKIGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4L6OFNJA3IQNRIGZ4DL6BWFA2WQOCYG2EDMKBWPC7TRLKIG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNPYGYUDK2BYLC7TRLKIG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLC7TRLKIG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA3IQNRIGZ4DNCBWFA3HRPZYVVEDL6BWFA2WQOCYG2EDMKBWPA27QNRIGVUDQWF7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6F7HCWUQNPYGYUDK2BYLA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBWRA3CQNTYX44K2SBV7A3CQNLIHBMDNCBWFA3HQNPYGYUDK2BYLC7TRLKIG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDL6BWFA2WQOCYG2EDMKBWPA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBMDL6BWFA2WQOCYX44K2SBV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBV7A3CQNLIHBMDNCBWFA3HQNUIGYUDM6F7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HRPZYVVEDNCBWFA3HQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBML6OFNJA3IQNRIGZ4DL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4L6OFNJA27QNRIGVUDQWF7HCWUQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPC7TRLKIGX4DMKBVNA4FQNUIGYUDM6F7HCWUQNPYGYUDK2BYLA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBWRA3CQNTYGX4DMKBVNA4FQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA27QNRIGVUDQWBWRA3CQNTYG2EDMKBWPA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA27QNRIGVUDQWBV7A3CQNLIHBML6OFNJA3IQNRIGZ4DL6BWFA2WQOCYGX4DMKBVNA4FQNUIGYUDM6F7HCWUQNPYGYUDK2BYLA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYGX4DMKBVNA4FRPZYVVEDNCBWFA3HQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BWRA3CQNTYX44K2SBV7A3CQNLIHBMDL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4L6OFNJA3IQNRIGZ4DNCBWFA3HRPZYVVEDL6BWFA2WQOCYGX4DMKBVNA4FRPZYVVEDL6BWFA2WQOCYG2EDMKBWPA3IQNRIGZ4DNCBWFA3HQNPYGYUDK2BYLC7TRLKIGX4DMKBVNA4FQNUIGYUDM6BWRA3CQNTYG2EDMKBWPA27QNRIGVUDQWF7HCWUQNPYGYUDK2BYLA3IQNRIGZ4DNCBWFA3HQNUIGYUDM6BV7A3CQNLIHBI=
(8217 bytes total)
File ASCII text dengan single line panjang berisi Base32-encoded data.
Key Insight
Multi-Layer Encoding: Base32 → CP932 (Japanese) → Morse Code → Base32 → Unicode Kanji → Byte Shift
Challenge ini menggunakan 6 layer encoding:
- Base32 decode → Japanese text (CP932 encoding)
- CP932 decode → Japanese characters yang merepresentasikan Morse code
- Japanese to Morse → Characters ツ (dash), ト (dot), ー (space)
- Morse decode → Base32 text
- Base32 decode → Unicode Kanji characters
- Byte extraction + shift → Extract low byte dari setiap Kanji, shift -9 → ASCII flag
Analisis:
- Hint "Japanese And 8000" mengacu pada CP932 encoding (Shift-JIS) dan range code points
- Three specific Japanese characters digunakan untuk represent Morse: ツ (-), ト (.), ー (space)
- Final layer menggunakan Unicode Kanji characters dengan low-byte encoding
- Byte shift of -9 applied to get final ASCII
Kesimpulan: Harus decode secara bertahap dengan memahami encoding Jepang dan Morse code mapping.
Solution Steps
Step 1 – Base32 Decode (Layer 1)
Decode Base32 string awal untuk mendapatkan Japanese text:
import base64
b32 = open("JP_8000.txt", "r", encoding="utf-8").read().strip()
raw = base64.b32decode(b32, casefold=True)
Step 2 – CP932 Decode (Layer 2)
Decode bytes sebagai CP932 (Japanese Shift-JIS encoding):
jp = raw.decode("cp932", errors="strict")
Hasil: Text berisi Japanese characters ツ, ト, dan ー
Step 3 – Japanese to Morse (Layer 3)
Convert Japanese characters ke Morse code:
ツ→-(dash)ト→.(dot)ー→
import re
morse = (jp
.replace("ツ", "-")
.replace("ト", ".")
.replace("ー", " ")
)
morse = re.sub(r"\s+", " ", morse).strip()
Step 4 – Morse Decode (Layer 4)
Decode Morse code ke Base32 text menggunakan standard Morse alphabet:
MORSE_TABLE = {
".-":"A","-...":"B","-.-.":"C","-..":"D",".":"E","..-.":"F",
"--.":"G","....":"H","..":"I",".---":"J","-.-":"K",".-..":"L",
"--":"M","-.":"N","---":"O",".--.":"P","--.-":"Q",".-.":"R",
"...":"S","-":"T","..-":"U","...-":"V",".--":"W","-..-":"X",
"-.--":"Y","--..":"Z","-----":"0",".----":"1","..---":"2",
"...--":"3","....-":"4",".....":"5","-....":"6","--...":"7",
"---..":"8","----.":"9","..--.-":"_","-.-.--":"!",".-.-.-":".",
"--..--":",","..--..":"?","-..-.":"/","-...-":"="
}
parts = []
for token in morse.split(" "):
if token and token in MORSE_TABLE:
parts.append(MORSE_TABLE[token])
b32_second = "".join(parts)
Step 5 – Base32 Decode Again (Layer 5)
Decode Base32 kedua untuk mendapatkan Unicode Kanji:
unicode_kanji = base64.b32decode(b32_second, casefold=True).decode("utf-8")
Step 6 – Byte Extraction and Shift (Layer 6)
Extract low byte dari setiap Kanji character, kemudian shift -9:
# Extract low byte (& 0xFF)
low_bytes = bytes((ord(ch) & 0xff) for ch in unicode_kanji)
# Shift -9
flag = bytes(((b - 9) & 0xff) for b in low_bytes).decode("ascii")
print(flag)
Solve Script
#!/usr/bin/env python3
import base64, re
# Step 1: Base32 decode
b32 = open("JP_8000.txt", "r", encoding="utf-8").read().strip()
raw = base64.b32decode(b32, casefold=True)
# Step 2: Decode as CP932 (Japanese Shift-JIS)
jp = raw.decode("cp932", errors="strict")
# Step 3: Japanese characters to Morse code
morse = (jp
.replace("ツ", "-") # dash
.replace("ト", ".") # dot
.replace("ー", " ") # space
)
morse = re.sub(r"\s+", " ", morse).strip()
# Step 4: Morse to text
MORSE_TABLE = {
".-":"A","-...":"B","-.-.":"C","-..":"D",".":"E","..-.":"F","--.":"G",
"....":"H","..":"I",".---":"J","-.-":"K",".-..":"L","--":"M","-.":"N",
"---":"O",".--.":"P","--.-":"Q",".-.":"R","...":"S","-":"T","..-":"U",
"...-":"V",".--":"W","-..-":"X","-.--":"Y","--..":"Z","-----":"0",
".----":"1","..---":"2","...--":"3","....-":"4",".....":"5","-....":"6",
"--...":"7","---..":"8","----.":"9","..--.-":"_","-.-.--":"!",
".-.-.-":".","--..--":",","..--..":"?","-..-.":"/","-...-":"="
}
parts = []
for token in morse.split(" "):
if token == "":
continue
if token not in MORSE_TABLE:
raise SystemExit(f"[!] Unknown Morse token: {token!r}")
parts.append(MORSE_TABLE[token])
b32_second = "".join(parts)
# Step 5: Base32 decode again to get Unicode Kanji
unicode_data = base64.b32decode(b32_second, casefold=True).decode("utf-8")
# Step 6: Extract low byte and shift -9
low_bytes = bytes((ord(ch) & 0xff) for ch in unicode_data)
flag = bytes(((b - 9) & 0xff) for b in low_bytes).decode("ascii")
print(flag)
Output:
FGTE{replace_dash_dot_space_japanes}
Conclusion
Challenge ini menggunakan 6-layer encoding dengan kombinasi unik:
- Base32 (standard encoding)
- CP932 (Japanese Shift-JIS encoding)
- Japanese characters as Morse (ツ=dash, ト=dot, ー=space)
- Morse code (International Morse alphabet)
- Base32 again (second layer)
- Unicode Kanji + byte shift (low-byte extraction with -9 offset)
Kunci sukses adalah mengenali encoding CP932/Shift-JIS dari hint "Japanese And 8000", mapping Japanese characters ke Morse, dan understanding low-byte extraction dari Unicode characters.
Pelajaran: Dalam multi-layer encoding challenge, perhatikan hints dalam nama challenge. "JP 8000" langsung mengarah ke Japanese encoding (CP932/Shift-JIS uses code points around 0x8000). Always consider cultural encodings seperti Shift-JIS, GB2312, Big5, dll dalam CTF.
More
Related in Cyber/CTF
Beberapa project lain di kategori yang sama.